Industrial automation devices control extremely critical and valuable assets, but all too often security is an afterthought in industrial networks. In the past, industrial operators trusted in their isolation, or “air gap,” from the broader network, the relative obscurity of their communications protocols, and the physical security of their facilities to protect the integrity of their networks. Now, in a changing, more connected world, automation network operators are realizing they must confront their unique security vulnerabilities. In a recent report prepared for the US Department of Homeland Security, security consultants InfraCritical found 500,000 exposed SCADA devices just by using a search engine, with 7,200 of those devices found to be controlling critical infrastructure assets such as water, energy, and other utilities. It’s not surprising, then, that security researchers characterize the state of ICS security as “laughable.”
Many industrial operators are not even aware the extent that their systems are exposed on the internet. The critical first step to closing the security gaps, then, is to acknowledge the existence of a vulnerability. But the next step is just as critical: the vulnerabilities must be completely addressed—and automation networks have three major unique vulnerabilities.
It Is Difficult to Secure Industrial Modbus TCP Protocol Packets
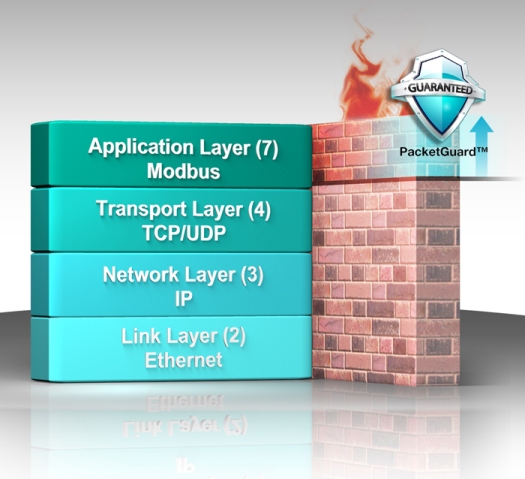
Even industrial networks that have moved to modern TCP/IP and Ethernet infrastructure for the transport, internet, and link layer of their communications are often still running industrial application layer protocols. The most popular of these, Modbus TCP, is also extremely vulnerable despite being widely used in industrial communications, with no built-in security systems at all.
This means that a packet that appears to be entirely legitimate when inspected as a TCP/IP packet—such as by checking its source IP address—may in fact contain malicious Modbus TCP communications that would be evident if the system were able to filter packets by Modbus source device ID, function codes, or other Modbus command type. Since industrial devices rarely have much in the way of application layer security, it’s up to the cyber security devices, such as hardware firewalls, to provide this critical missing protection. Unfortunately, conventional firewall solutions rarely include the technology to scan industrial protocols such as Modbus TCP.
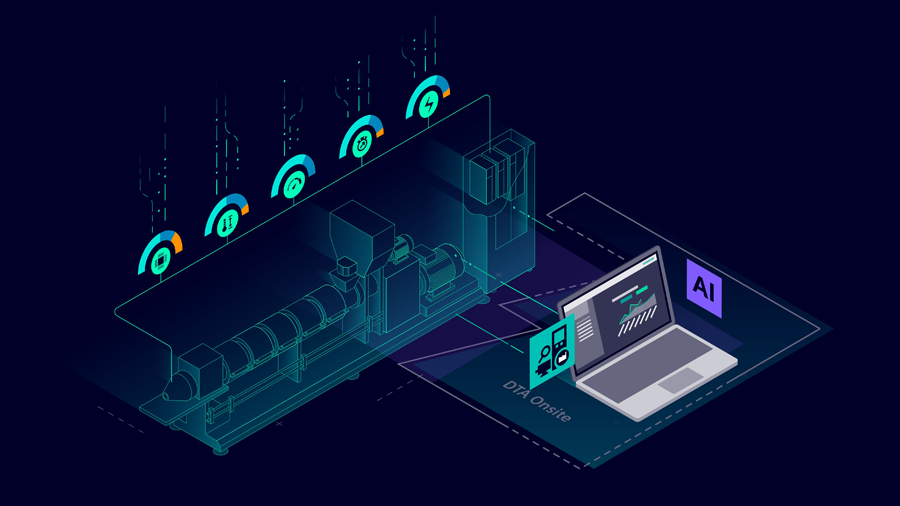
Industrial Applications are Time-Critical and Can Not Tolerate Transmission Delay
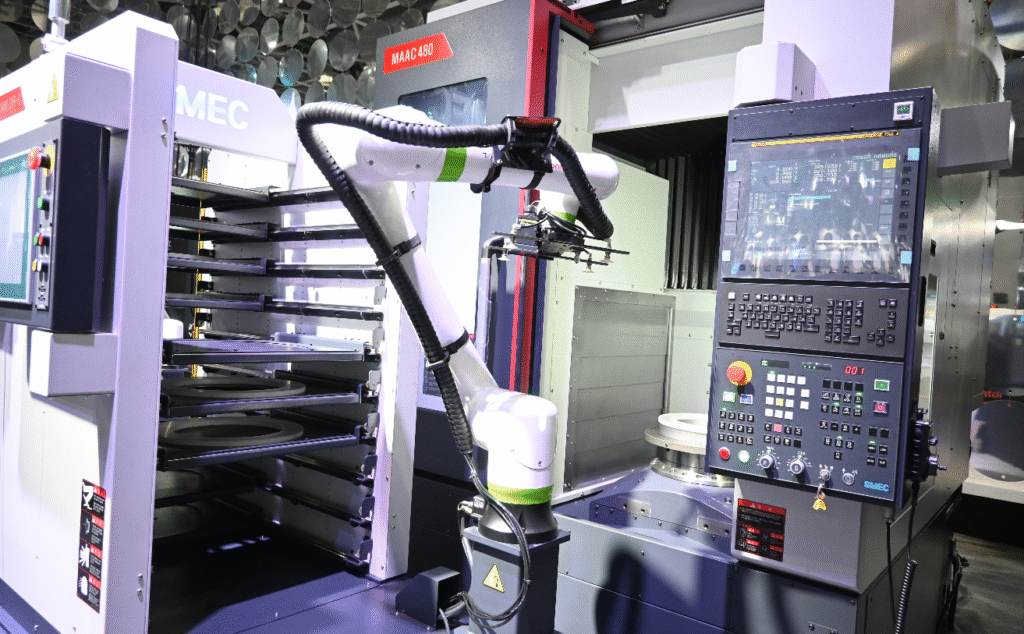
SCADA and industrial control devices directly manage real-world machinery in a way that is highly time-critical. For example, on an assembly line, all of the different machinery needs to operate in perfect coordination in order for the line to keep moving. Electric substation operations are even more time-sensitive, as a delay in triggering a circuit switch could create a power fluctuation or even a blackout.
The highly time-critical nature of industrial operations means that industrial networks can not tolerate significant latency issues. However, a common assault vector used by malicious attackers is to overwhelm a network with requests, which can affect the network latency even if a firewall is able to block the unauthorized requests. Insufficient bandwidth during critical moments will also expose the network to latency issues if the firewall is struggling to process packets quickly enough to maintain timely communications.
The latency and network demands on industrial security will only grow as industrial networks become more advanced and begin to integrate more systems ,such as video, voice, and data. IP cameras generate a lot of bandwidth, and the network security devices need to have the bandwidth and throughput to support advanced applications without compromising the security of the network or the latency of other industrial operations.
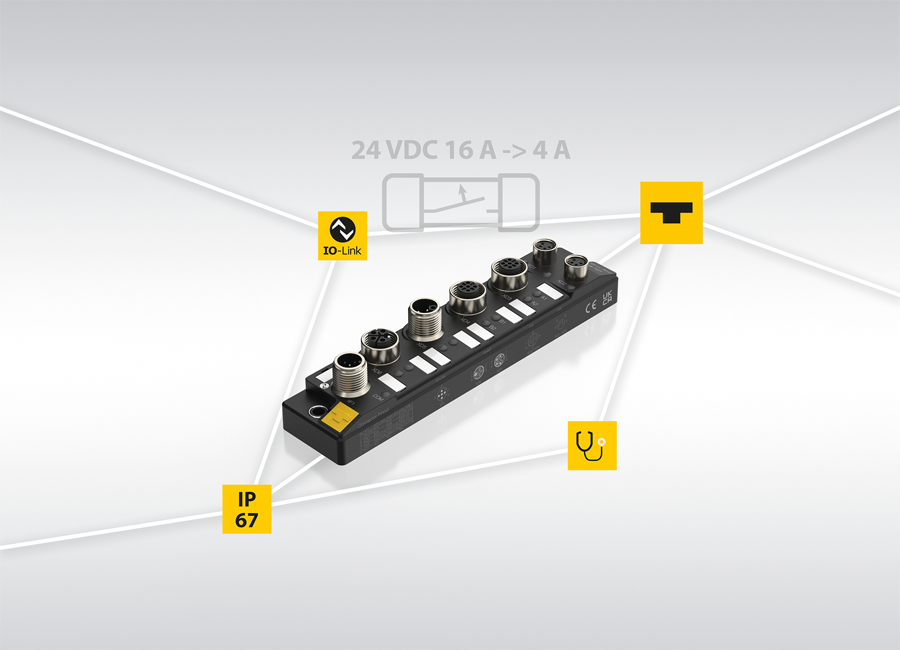
Demanding Physical Environments can Overwhelm Security Devices
Industrial machinery and industrial control devices are deployed in more extreme conditions than most conventional IT network equipment. This presents a potential mismatch in the performance of industrial control devices and the network security devices that are intended to protect them—the network security devices might struggle to hold up in the sort of intense industrial conditions that industrial automation systems must operate in. Harsh environmental hazards such as extreme temperature, EMC, and EMI, can be even more damaging to network equipment than a malicious attacker. If the network security hardware is not able to shrug off these hazards, the network will remain exposed and vulnerable to attackers.
Moxa has combined its background in industrial automation with its expertise in networking to create a cyber security solution that was designed with the unique needs and requirements of automation networks in mind. The Moxa EDR-810 is an industrial multi-port secure router that includes security functionality and is specifically optimized to address the security vulnerabilities of industrial networks. In addition to a VPN that encrypts data tunnels for remote access, a NAT to hides local IPs, and a firewall that filters packets, the EDR-810 adds automation-friendly functions such as:
Deep Modbus TCP inspection: PacketGuard™, is the world’s first built-in Modbus TCP packet inspector. With PacketGuard, the EDR-810 will inspect network packets all the way up to the Modbus application level, deeper than the transport-layer scanning that conventional network firewalls can achieve.

Low latency gigabit performance: The EDR-810 can aggregate its many ports into a Gigabit uplink, for extremely low latency performance that will not interrupt industrial operations, even when used in extremely bandwidth-hungry applications such as IP video.
Highly integrated multi-port secure router with switch functions: The EDR-810 combines security, routing, and layer 2 switch functionality into a single device, making it a highly convenient and cost-effective solution that connects and protects many devices.
The EDR-810 is the latest in Moxa’s EDR family of network security devices tailored for industrial operators. Wide operating temperature range, hardened metal housings, and strong EMI/EMS resistance give Moxa’s EDR security devices the resilience to stand up to harsh operating conditions and keep up with robust industrial networks. For all the details about this entire line of advanced network security hardware, visit http://www.moxa.com/product/Industrial_Secure_Routers.htm
[ICNweb www.icnweb.kr]








![[#HM26] 협동로봇의 진화, ‘보조’ 넘어 ‘산업용 핵심’으로 [#HM26] 협동로봇의 진화, ‘보조’ 넘어 ‘산업용 핵심’으로](https://icnweb.kr/wp-content/uploads/2026/05/HM26_fanuc_cobot-900web.png)










![[그래프] 국회의원 선거 결과 정당별 의석수 (19대-22대) 대한민국 국회의원 선거 결과(정당별 의석 수)](https://icnweb.kr/wp-content/uploads/2025/04/main-image-vote-flo-web-2-324x160.jpg)