Production facilities and components of Industry 4.0 are linked to the Internet, networked with each other, and thus open to attack. Using an IT security laboratory, Fraunhofer researchers offer a test environment in order to simulate attacks on this network and to detect any gaps. From April 13 to 17 they will unveil the possibilities at this year‘s Hannover Messe (Hall 2, Booth C16).
![[HannoverMesse] Safe production in Industry 4.0 [HannoverMesse] Safe production in Industry 4.0](https://icnweb.kr/wp-content/uploads/2015/04/Fraunhofer_apmbild-10128207-600x600-367536.jpg)
Beautiful new production world: For value-creation chains that span multiple locations, equipment, robotics, systems components, minicomputers in components and sensors are all networked with each other in Industry 4.0. They exchange data, retrieve the status of equipment and components, calculate the optimal sequence of work processes, schedule equipment usage and much more. Yet with the entry of communications into factories via Internet technologies, the safety risk also increases. Beside the known viruses, there are new, custom-tailored malware programs threatening the networked production plants. They can spy out system parameters, remotely control machinery, manipulate controls or paralyze processes. Industry 4.0 networks therefore require particular protective measures, sophisticated network technology and effective test methods that detect security gaps and close them reliably. With an IT security laboratory specially equipped for production and automation technology, the Fraunhofer Institute of Optronics, System Technologies and Image Exploitation IOSB in Karlsruhe provides a secured test environment in order to readjust potential attacks on production networks, to study the effects and thus, to deduce new strategies and suitable defense measures. It also enables researchers to assess the security functions of conventional communications standards and protocols for industrial automation systems. These regulate, among other things, the data encryption to counter product piracy, espionage and sabotage.
Different framework conditions than in office IT
“IT security in industrial production must take into account entirely different framework conditions that do not exist accordingly in Office IT,” says Birger Krägelin, project manager at IOSB’s IT Security Laboratory. The control of production facilities entails real time requirements that make changes to the systems diffi cult. Downloading available software patches onto the systems and installing surveillance software, malware scanners, and antivirus programs influence the stability of meticulously coordinated processes. By the same token, production processes affect conditions when updates can be realized. Firewalls within the network and encrypted connection between systems can diminish real-time conditions. “For example, it is possible that the built-in of known security measures from the offi ce environment can delay the dispatch of messages between computers. That can lead to conveyor belts running slower, valves or outlets closing with a delay, light barriers are triggered incorrectly, the rotational speed of motors increases, or control components break down,” Krägelin explains. Even the relatively long usage period of hardware and software in production is markedly different from other areas where IT is deployed.
In order to find and establish appropriate IT security mechanisms for the production environment, the research team of specialists in automation technology and IT security equipped the laboratory accordingly. It features its own model factory with real automation components that control a simulated production facility, complete with conveyor belts, electric motors, robots, and lifting equipment. All network levels of a factory are equipped with typical components, including fi rewalls, circuits, and components for wireless parts. Having its own private cloud means it is possible for the IOSB experts to fl exibly arrange various configurations and set up the model factory for a variety of scenarios.
“In the cloud, we can patch in virtual firewalls, PCs, add additional client computers and modify entire network structures with just one mouse-click. This makes it possible for us to install a virtual fi rewall or even analytical systems between two components, such as a machine and an overarching MES system (Manufacturing Execution System). From the cloud, we can start malware detection and for example text controls and systems visualizations for infections,” the master of information science (MIS) explains. “We are capable of building other factory situations and simulate cyber attacks – without having to buy components and configure circuitry.”
The researchers from IOSB will be demonstrating which attack scenarios could happen to networked production facilities at the Fraunhofer joint exhibition booth at this year’s Hannover Messe, in Hall 2, Booth C16 from April 13 to 17. Companies can use the laboratory so they can consult on the planning and operational launch of secure industrial network structures. In addition, they benefit from the know-how of the IOSB experts when it comes to the analysis of their already existing network and components. Furthermore, the researchers want to offer the laboratory in the future as an education and learning platform for training measures. “The one thing that engineers often don’t have is the knowledge of how to deal with cyber threats,” Krägelin points out.
www.icnweb.co.kr
[HannoverMesse] Safe production in Industry 4.0
뉴스레터 구독하기
아이씨엔매거진은 AIoT, IIoT 및 피지컬 AI, 디지털트윈을 통한 제조업 디지털전환 애널리틱스를 제공합니다.
테크리포트: 자율제조, 전력전자, 모빌리티, 로보틱스, 스마트농업
구글, 엣지 AI 혁신 이끌 ‘젬마 4’ 공개… 온디바이스 추론 성능...
구글이 인터넷 연결 없이도 스마트폰이나 소형 산업용 컴퓨터에서 빠르게 작동하는 인공지능 '젬마 4'를 공개했다. 이 모델은 크기가 작으면서도 성능은 대형 AI 못지않아 공장의 기계 상태를 살피거나 로봇을 조종하는 데 유용하다
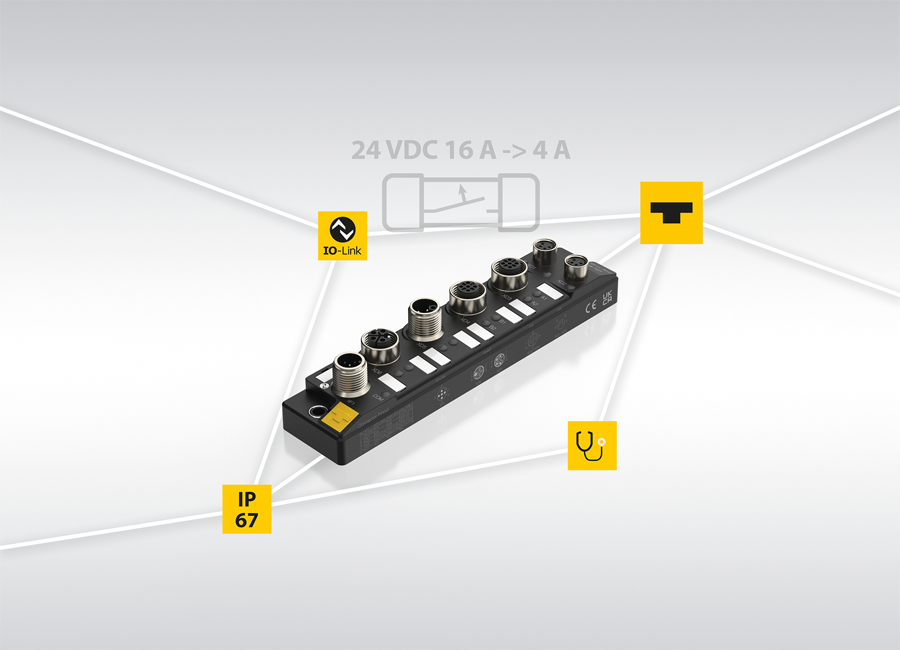
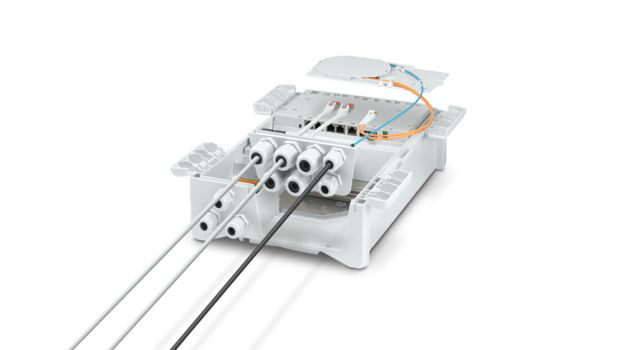
피닉스컨택트, 유지보수·보안성 강화한 실외용 스마트 이더넷 박스 출시
피닉스컨택트가 실외에서 사용하는 똑똑한 통신 상자인 스마트 이더넷 박스를 업그레이드했다. 가장 큰 장점은 고장이 났을 때 복잡한 광케이블을 다시 연결할 필요 없이 상자 본체만 갈아 끼울 수 있어 복구 시간이 매우 짧다는 것
[#HM24] 안전한 데이터 교환의 상생적 이점
Roseman Labs의 솔루션은 실제 데이터의 개인 정보와 상업적 민감성을 보존하면서 여러 데이터 세트를 암호화, 연결 및 분석할 수 있도록 한다
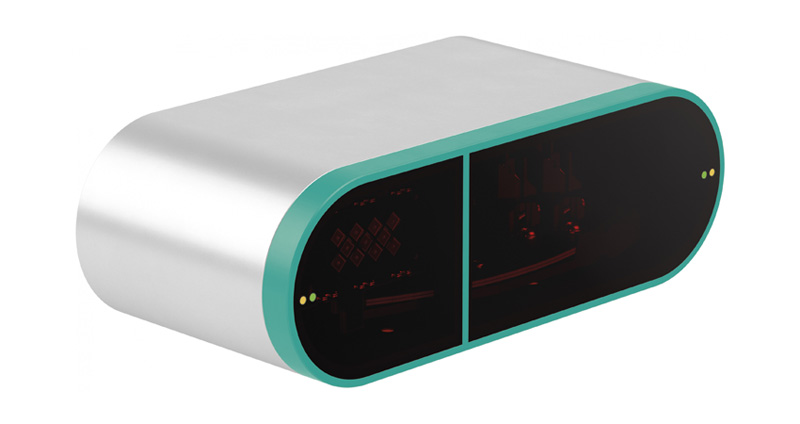
P+F, LiDAR와 MEMS 결합한 산업용 3D 센서 개발
P+F와 프라운호퍼 연구소는 지난 4월말 독일에서 개최된 하노버산업박람회(Hannover Messe 2023)에서 LiDAR와 MEMS 기술을 결합해 개발한 R3000 3-D LiDAR/MEMS 센서에 대한 연구 사례를 발표했다.
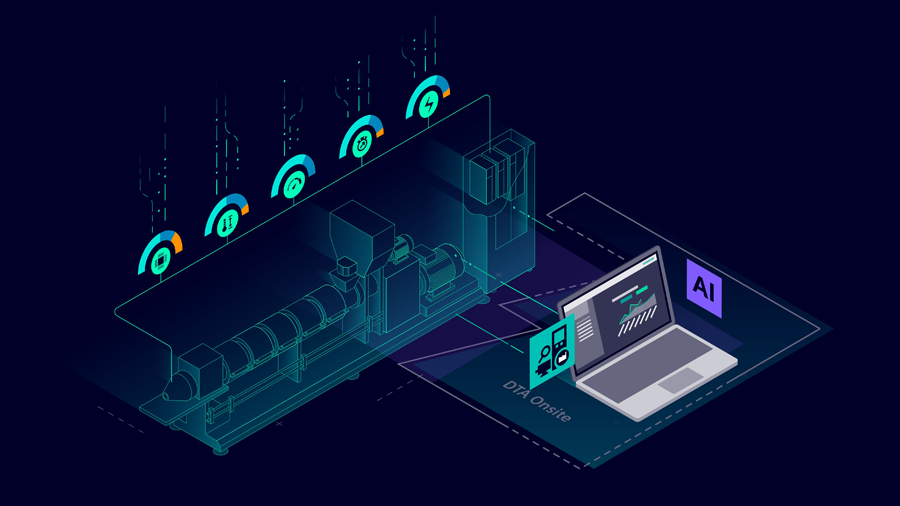
[#HM24] 벡호프, AI 모델 생성을 간소화하는 AutoML 도구 출시
AutoML은 규제 산업에서 설명 가능하고 재현 가능한 결과를 제공하는데 AI 솔루션을 제공한다는 유망한 전망을 제시하고 있다








![[전문가기고] K-배터리 3사, ‘Beyond EV’ 시장을 향한 기술 초격차 전략 비교 [인터배터리 2026] [전문가기고] K-배터리 3사, ‘Beyond EV’ 시장을 향한 기술 초격차 전략 비교 [인터배터리 2026]](https://icnweb.kr/wp-content/uploads/2026/03/battery-P3-beyond-Battery-web-1024x576.png)
![[심층기획] 피지컬 AI의 심장 ‘이차전지’, 휴머노이드 로봇 혁명 이끈다 [인터배터리 2026] [심층기획] 피지컬 AI의 심장 ‘이차전지’, 휴머노이드 로봇 혁명 이끈다 [인터배터리 2026]](https://icnweb.kr/wp-content/uploads/2026/03/Battery-pack-interB-Phy-AI.png)






![[칼럼] 제조업 생존 가르는 EU CRA와 피지컬 AI 보안 전략 [칼럼] 제조업 생존 가르는 EU CRA와 피지컬 AI 보안 전략](https://icnweb.kr/wp-content/uploads/2026/03/CRA-2026-notebookLM-20260326-1024web.png)


![[그래프] 국회의원 선거 결과 정당별 의석수 (19대-22대) 대한민국 국회의원 선거 결과(정당별 의석 수)](https://icnweb.kr/wp-content/uploads/2025/04/main-image-vote-flo-web-2-324x160.jpg)

![[#HM24] HARTING, 미래 핵심인 전기에너지에 열정을 쏟다 [#HM24] HARTING, 미래 핵심인 전기에너지에 열정을 쏟다](https://icnweb.kr/wp-content/uploads/2024/04/HM24-HARTING_TECO-2030-900web.jpg)
![[#HM24] 안전한 데이터 교환의 상생적 이점 [#HM24] 안전한 데이터 교환의 상생적 이점](https://icnweb.kr/wp-content/uploads/2024/04/roseman-labs-hm24_3_2-1024x683.jpg)

![[#HM24] 벡호프, AI 모델 생성을 간소화하는 AutoML 도구 출시 [#HM24] 벡호프, AI 모델 생성을 간소화하는 AutoML 도구 출시](https://icnweb.kr/wp-content/uploads/2024/04/TwinCAT-ML-Creator-Dr-Fabian-web.png)